The potential impact of a cyberattack on a smart electricity distribution system can be illustrated in a simple example. Let us assume simple 4-bus low voltage distribution system including two loads and two solar photovoltaics (PV) generators.
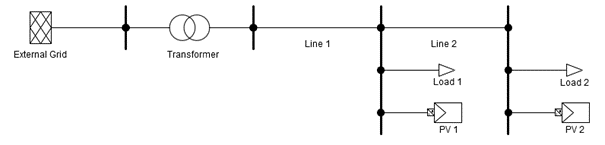
We make two further assumptions:
- Both PV units are not only intended to supply energy to their corresponding loads, but are meant to feed excess energy into the grid. They have been installed with sufficient power capacity that the current loading of the transformer will exceed its permitted upper limit if the total consumer load drops to zero around noon on a sunny day, when the PV units generate power at their maximum capacity.
- The system operator uses Smart Grid technology to monitor and (if necessary) control the DER in this distribution system. It would temporarily limit the permissible power output of the PV units in the described situation to avoid the transformer overloading.
What happens if the communication system fails and the PV units can no longer send or receive data? This can happen for multiple reasons including simple technical failure, but it can also occur as a result of a cyberattack on a router. In any case the result must never be the transformer overloading.
One problem here is that it is not possible to detect the overloading of the transformer through measurements taken at the buses where the users and PV units are connected.
The DER control system therefore must be designed to track the status of the bidirectional communication channel to the system operator to prevent the problem from occurring. If this channel is interrupted or disturbed for any reason, then the output of each PV system must be limited to a value known to be acceptable under any conditions. This value can either be:
- a fixed value agreed with the system operator during the connection process, or
- it could be the power consumed by the local load.
It is also possible to configure the PV unit to completely disconnect in such a situation, although this would be less attractive economically because all the power to supply the local load would then temporarily have to be drawn from the grid. In either case all of this would have to happen automatically without human intervention, since permanent human supervision is not an economically feasible approach in medium voltage and low voltage distribution systems.
The above is only one scenario that needs to be covered to achieve a resilient system. Instead of only disabling communication, attackers may also take control of one or more DER and force them to disobey control signals. More elaborate answers need to be developed to mitigate such cases. SDN technology offers an approach to address such issues on the communication network layer.
SDN-microSENSE Threat Mitigation Toolbox
SDN technology allows rerouting data traffic within a physically redundant communication network. Based on this principle, both monitoring data and control signal data can be rerouted around compromised communication equipment, allowing effective mitigation of attack impact, prevention of attack proliferation, and fast restoration of observability and controllability. The SDN-microSENSE toolbox in addition to this provides further tools to detect and classify attacks and their corresponding risks, and even includes mechanisms to isolate entire grid segments from the impact of some cyberattacks where useful.