Different honeypot projects/concepts have emerged in recent years aiming to protect and secure industrial control systems (ICSs). The honeypots are evolving and being used as honeynets; a network of honeypots interacting with the environment as one entity, thus collecting even more knowledge about the incoming attacks. To predict future attacks and increase the level of response to incidents, it is very important to obtain all relevant information on potential attackers, their methodology, potential targets or systems of interest.
Honeypots in ICS
A honeypot is a useful tool to enhance control system security as it appears to contain information or resources of value inside the network, but actually, is isolated and monitored allowing the collection of information that can analyze the behavior of the attackers. Conpot is the ICS/SCADA server honeypot run by the development team of Conpot and The Honeynet Project [RIS13]. Conpot’s key advantage is that it can easily be updated, extended and deployed. A Siemens SIMATIC S7-200 PLC with basic functions, an input / output module and a Communication Processor CP 443-1 is used to simulate the basic configuration which allows connection to SIMATIC via ethernet [RIS13]. Conpot can also be linked to an actual HMI and enables the interaction with real ICS hardware. The software supports standard protocols for industrial management such as Modbus, HTTP, S7Comm, IEC104, SNMP, CIP, Ethernet/IP, BACnet and IPMI.
The ICSs consist of many types of control systems, including SCADA, Remotes Terminal Units (RTUs), Human Machine Interface (HMI), etc. EPES systems include industrial processes, corporate network services (web services, email, storage services, etc.), supervision systems (SCADA, etc.) and a series of industrial controlling devices such as programmable logic controllers (PLCs) and distributed control system (DCS). The industrial process is controllable by means of a control network, which enables information transmission to the RTU using industrial communication protocols (Modbus, IEC104, etc.) by wired or wireless means through HMI and control of industrial devices capable of opening or closing breakers and connectors.
Description of the IEC 60870-5 protocol
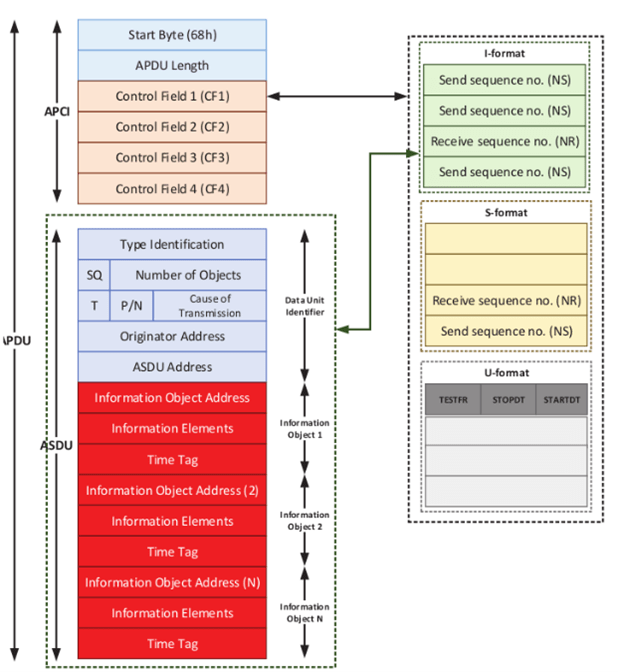
IEC-104 [UOWM3] belongs in the IEC 60870-5 set of communication protocol that uses the TCP/IP transport capacities to track and manage automatic processes for the EPES applications. Typically, the TCP port 2404 is used by default. This protocol called Application Protocol Data Unit (APDU) and it is illustrated in Figure 1.
APDU includes two parts
1. Application Protocol Control Information (APCI)
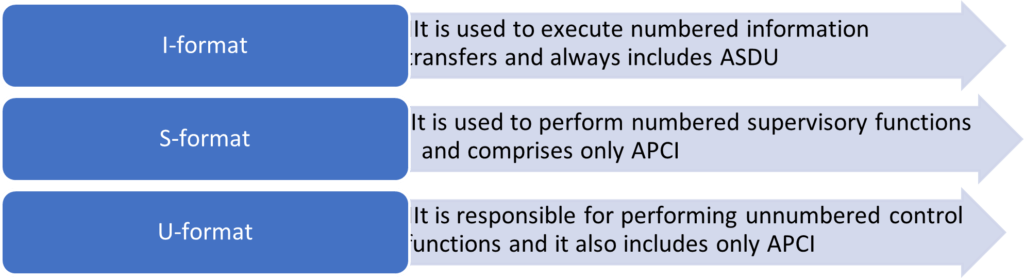
APCI includes the start character (68h), the length of APDU and four Control Fields (CFs). In particular, APDU can take three formats as shown in Figure 2.
The CF1 and in particular the last two bits define the APDU format. The I-format is used if the two last CF1 bits equal to 00. Therefore, the S format shall be implemented, if the last bits of CF 1 are equal to 01. Finally, the U-format is used if the above bits are 11.
2. Application Service Data Unit (ASDU)
ASDU is an optional part which is determined by the format of APDU. The Type Identification field determines the type of information objects. All information objects of an ASDU must have the same type
The functionality of the IEC-104 protocol relies on the TCP/IP, which itself includes multiple security issues. Moreover, IEC-104 does not include any authentication and authorisation mechanism, thus enabling potential Man-in-The-Middle (MiTM) and unauthorised attacks.
Honeypot IEC60870-5-104 in SDN-microSENSE
Conpot honeypot supports IEC 60870-104[60870] for the monitoring, control and communication of energy systems. We use the RTU honeypot in SDN-microSENSE to imitate the actions of an RTU which control systems in an intelligent grid substation. In the controlling direction, more system information communications commands such as the counter interrogation command and the read command were added to the Conpot honeypot. It is a serial asynchronous protocol and is used for tele-control. It offers TCP/IP features and allows LAN network connectivity. An RTU device can function in real production systems as a master or as a slave. Therefore, the same action is imitated in an RTU honeypot.
References
[UOWM3] Radoglou-Grammatikis, P., Sarigiannidis, P., Giannoulakis, I., Kafetzakis, E., & Panaousis, E. (2019, July). Attacking IEC-60870-5-104 SCADA Systems. In 2019 IEEE World Congress on Services (SERVICES) (Vol. 2642, pp. 41-46). IEEE.
[MANOUSEK2019] Matoušek, P., Ryšavý, O., & Grégr, M. (2019, September). Increasing Visibility of IEC 104 Communication in the Smart Grid. In 6th International Symposium for ICS & SCADA Cyber Security Research 2019 6 (pp. 21-30).
[RIS13] L. Rist, “Introducing Conpot,” 2013. [Online]. Available: Https://www.honeynet.org/node/1047
[60870] IEC 60870-5-104:2006+AMD1:2016 CSV – Telecontrol equipment and systems – Part 5-104: Transmission protocols – Network access for IEC 60870-5-101 using standard transport profiles.